Retrace Azure Integration
Overview
Retrace integrates with Azure via the Azure Rest API to determine the status of servers and services during Creation, Removal, Scale Up and Scale Down events. Retrace supports monitoring for both Cloud Services (Classic) and App Services (Web sites, Functions, etc..).
To acquire resource information Retrace uses OAuth 2.0 Access Tokens on the Azure account to authenticate and make calls to the Azure Rest API.
Prerequisites
In order to successfully monitor your Azure services Stackify recommends using a dedicated service account rather than an individual user’s account. That account needs to be a Work or School account and have access to the subscriptions and services that you want to monitor.
Personal Azure accounts are not supported since they do not use Azure Active Directory.
Retrace also requires the installation of the Retrace Agent on your Cloud Services or the Stackify Web Job on your App Services.
Setup
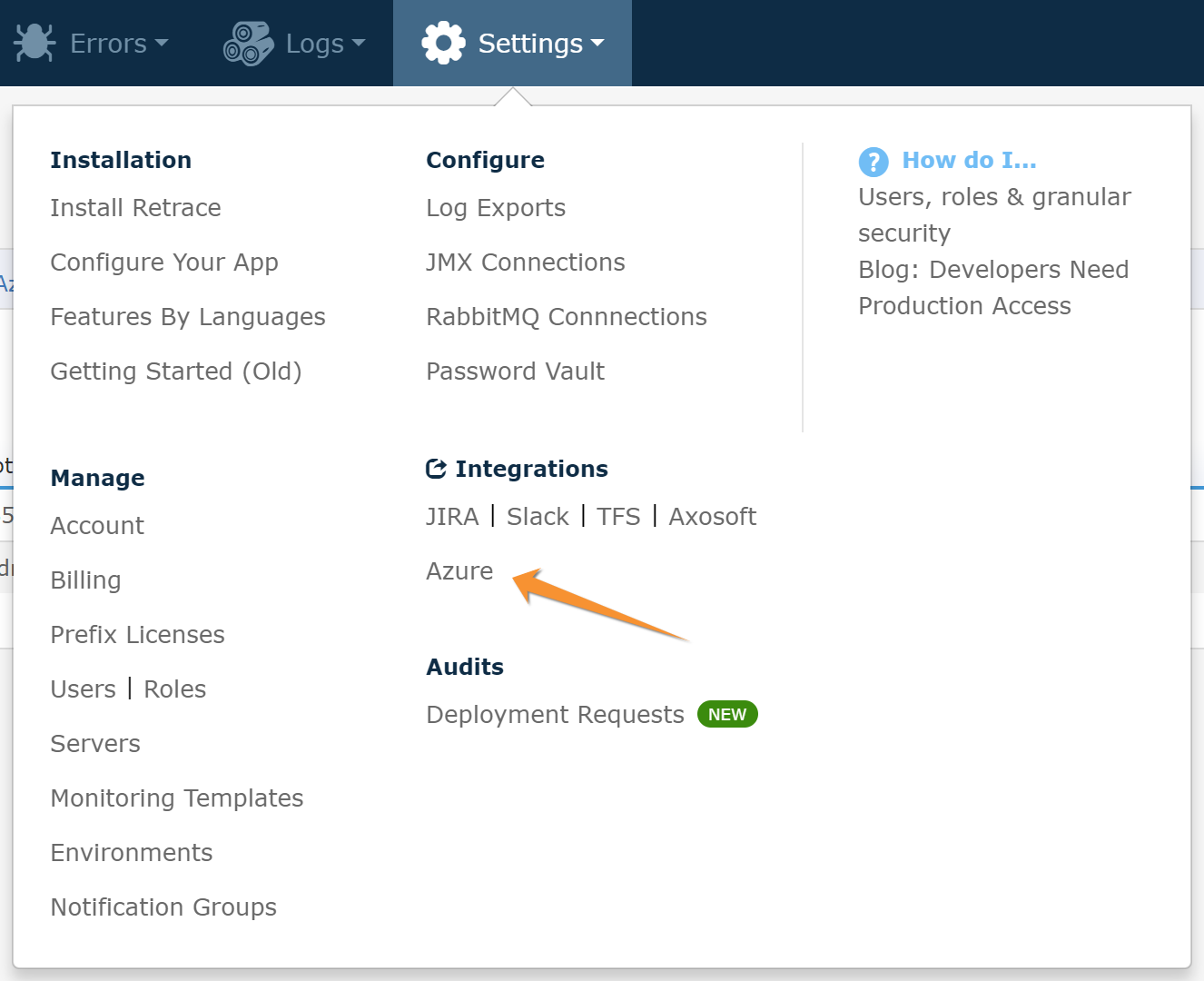
To setup monitoring, login to your Retrace account and navigate to the Azure page of the Integrations section under Settings. You will need to be an Account Admin in order to access this page.
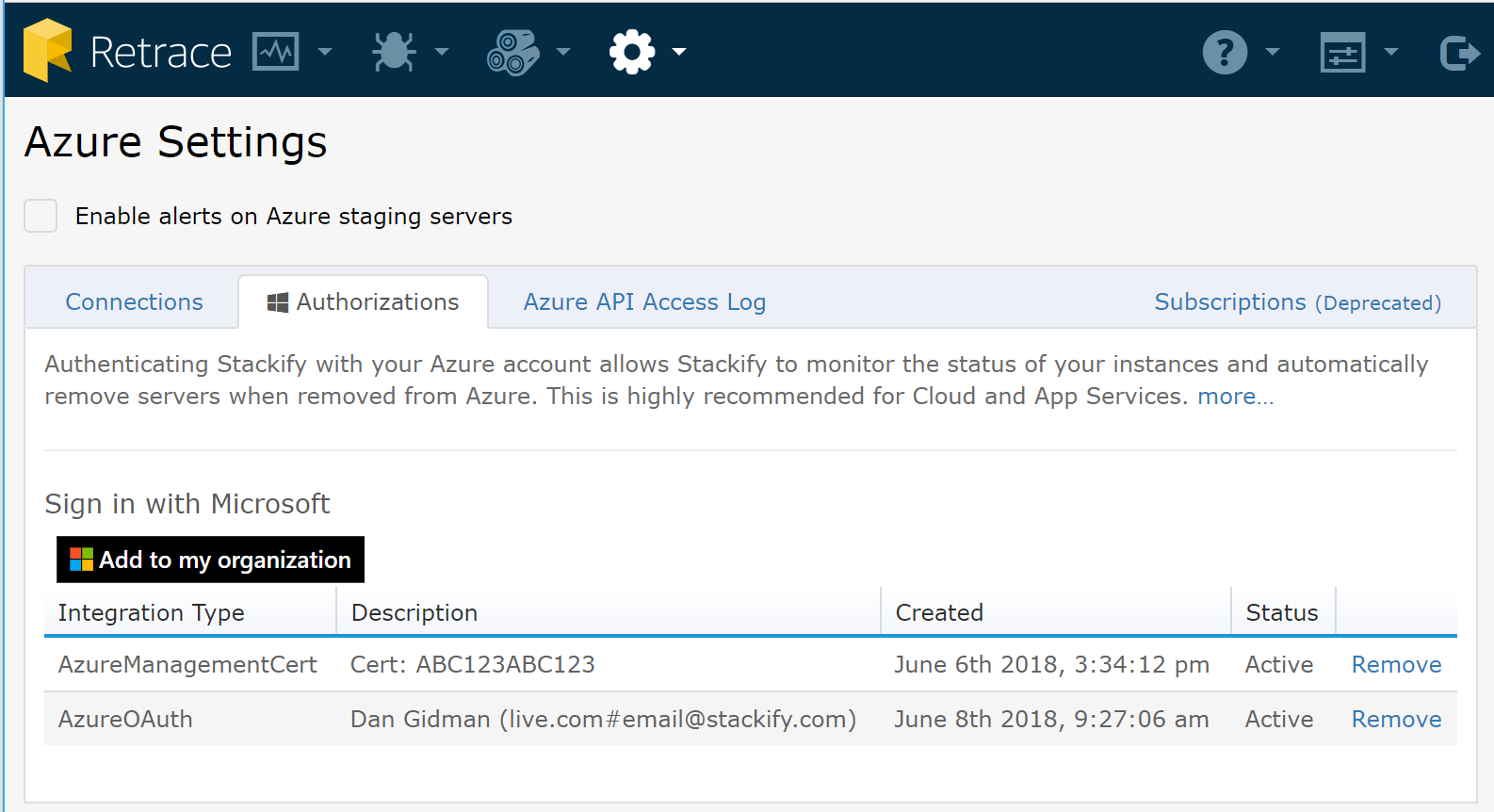
On the Azure Settings page, select the Authorizations tab. Here you will see a list of integrations that have been created. Click the Add to my organization button to begin the authorization process.
After clicking Add to my organization you will be directed through a Microsoft login and authorization process and be prompted to allow Retrace to access your data.
Once you allow Retrace to access your data you will be redirected back to Retrace. Retrace will now be able to query Azure Rest API for the state of your services and devices.
The Azure provided access token will allow access only to resources that the provided account has access to. This is why using a service account that is given permissions only to resources you may want to monitor is recommended.
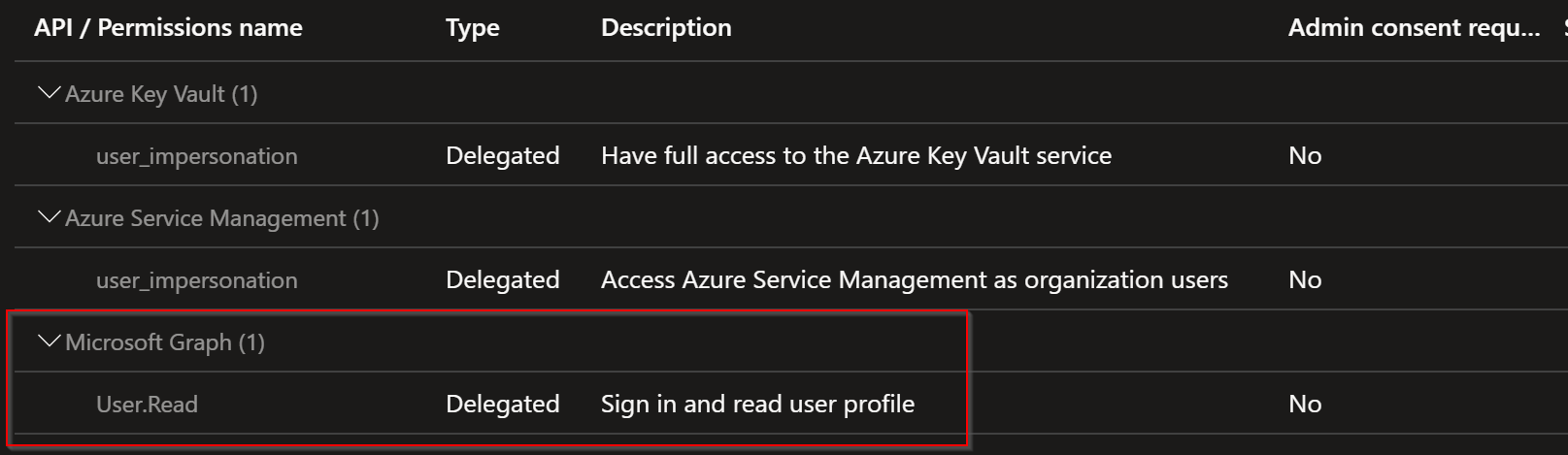
Ensure that Stackify has User.Read API Permission access granted for Microsoft Graph:
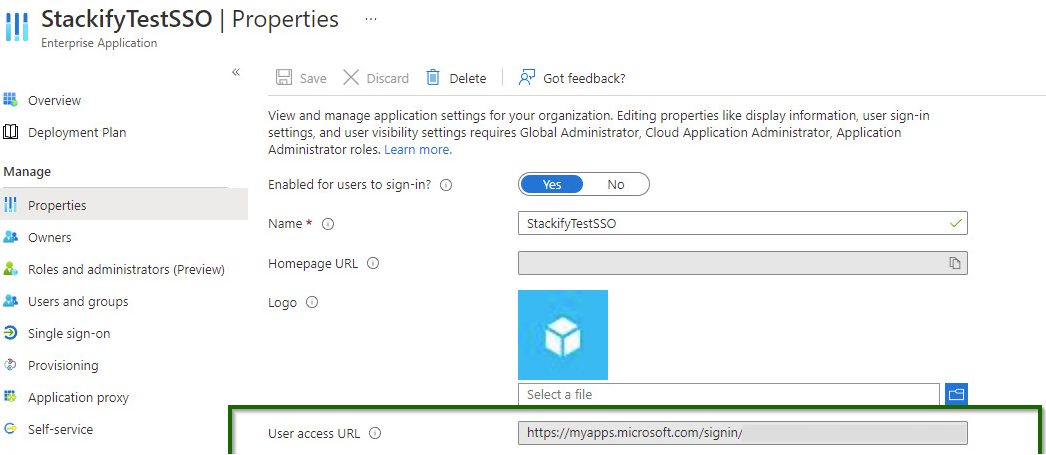
When logging in from your Azure SSO you need to use the "My Apps" page in Azure.
Or when using the direct URL you must use the "User Access URL" of the app.
Monitoring Retrace Access
Logs
The Azure Settings page provides a 7 day log of every access attempt Retrace made to Azure on your behalf. Reported is the date and time of access, the uri, account and the returned status code of the request. You can find this under the Azure API Access Log.
Remove Access
To disable access, go to the Authorizations tab and click Remove next to the authorization you wish to remove.
Legacy Support
Customers who had setup the now deprecated method of Azure Integration (*.publishsettings) will see that integration listed as the AzureManagementCert integration type. It is recommended that you remove this and set up the integration using the current supported method. Support for the AzureManagementCert integration type will be removed at a future date.